What is Behavioral Biometrics?
Manage fraud risk and improve user experience with Arvato Financial Solutions’ Behavioral Biometrics solution.
Recognise the legitimate user – continuously and without friction
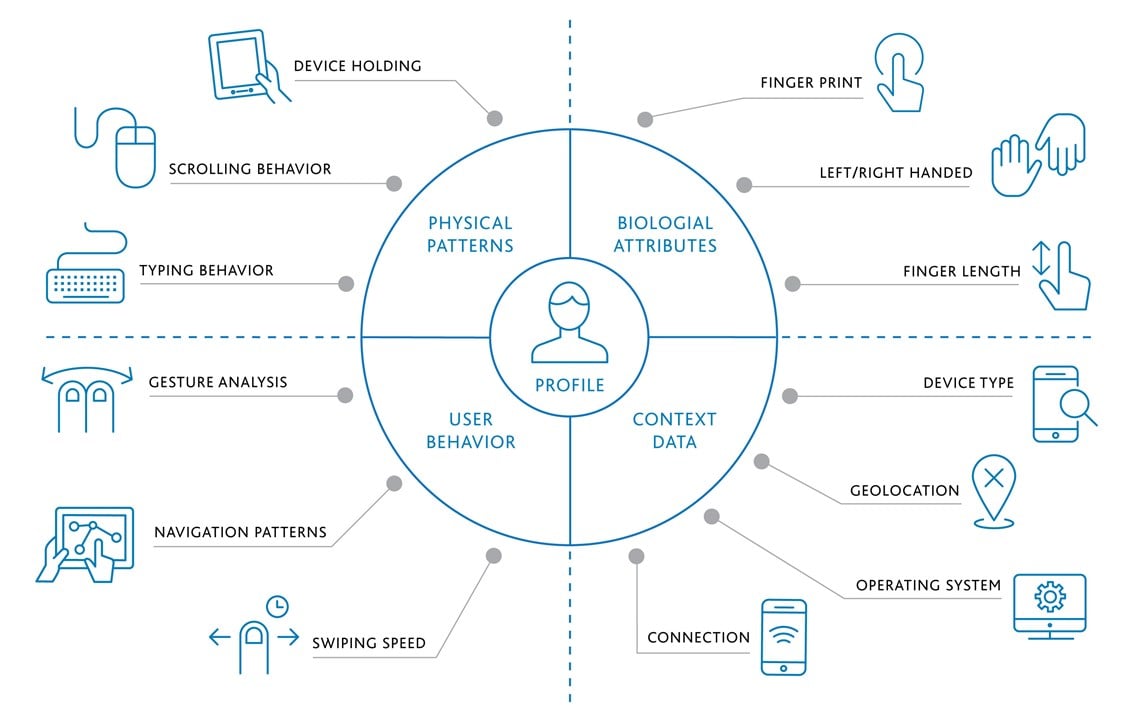
Authenticating the legitimate user protects customer accounts from fraudsters. Unlike conventional authentication methods which rely on what the user knows (e.g. passwords) or has (e.g. tokens), Behavioral Biometrics focuses primarily on the analysis of physical and behavioral parameters, which can’t be stolen. It has no hardware or personal data dependency and is PSD2 compliant.
Acting as an invisible two factor authentication, Behavioral Biometrics ensures a frictionless authentication process and prevents fraud:
- Identity fraud (through methods such as phishing, social engineering and automated attacks to conduct)
- Account takeover (when someone uses another person’s account with stolen credentials)
- Payment fraud (to protect the payment information linked to the users accounts)
- Automated attacks (recognizing non-human device activity e.g. BOTS (network of infected devices controlled by unautorized third party), RATs (remote access trojans) and emulators (e.g. software which masks non-mobile devices to appear as such applied for adfraud))
Advantages of a frictionless user authentication
The big advantage of Behavioral Biometrics is the continuous and frictionless user authentication in real time. The analysis is dynamic and takes place during the entire session from login to logout, without the user having to prove that he is the actual account holder.
by strengthening security with seamless authentication for your customers powered by biometrics to have an optimal user experience
detecting fraud attempts through continuous monitoring through the complete session– from login to logout
threats through recognition of emulators and non-human behavior such as BOTs or RATs
Clearly differentiate between good users and fraudsters. Accept or block transactions accordingly and reduce manual reviews
Especially accurate thanks to the analysis of more than 100 different behavioral parameters
through the creation of unique user profiles for each member to ensure the legitimacy of the transactions
through the implementation of an invisible two factor authentication, reducing the need of offering active authentication methods (e.g. tan, cvv, sms)
Our solution
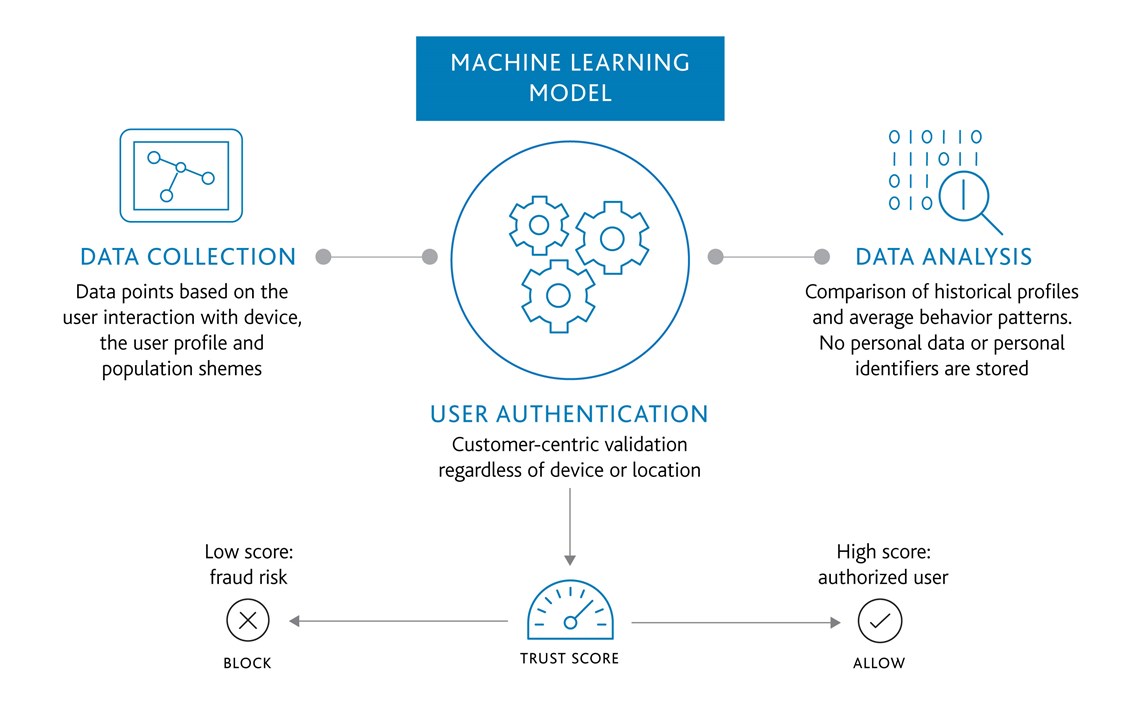
To autheticate the user, Behavioral Biometrics analyzes more than 100 physical behavioral parameters, such as user finger pressure on a mobile device, fingertip size, touch coordinates and device movement, in order to generate a unique profile for each user.
Thanks to machine learning algorithms, the solutions continuously monitors and improves accuracy and gets to know a multitude of behavioral patterns of a person. Everything is analysed in the background, which dynamically improves security and accuracy.
The passive biometric authentication and analysis of user behavior do not only recognise the legitimate user but also allow distinguishing between human and automated fraudulent activities.
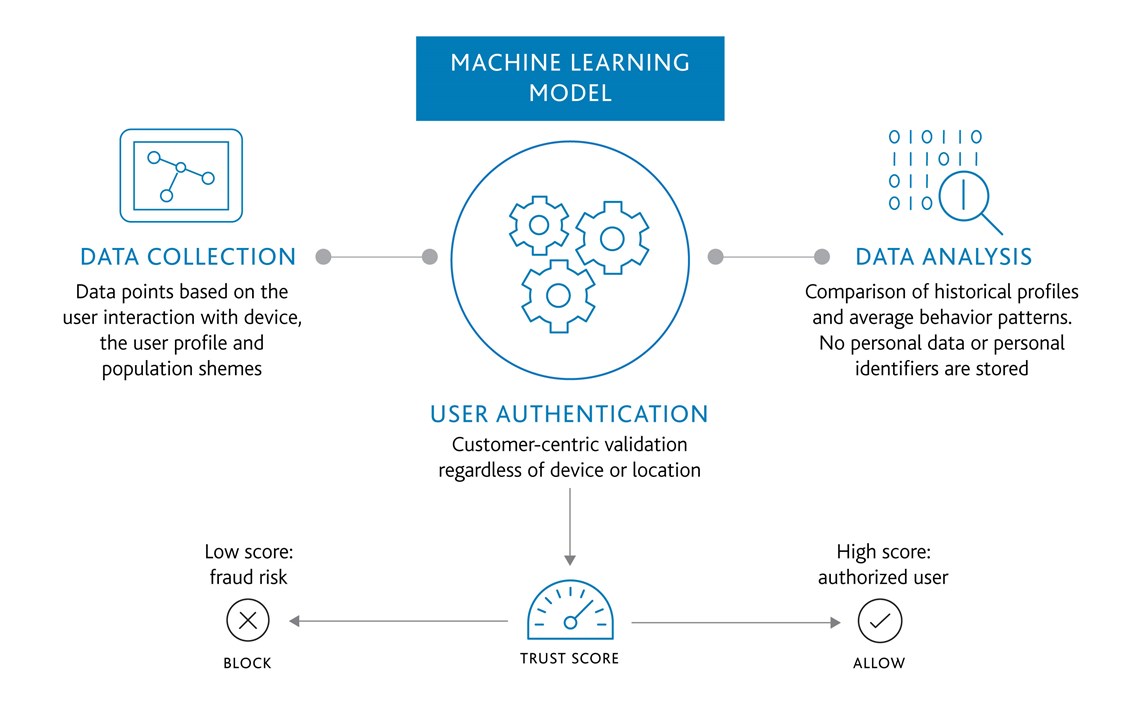
Confidence scoring for user validation